SYN Flood Attacks Have Reached its Highest Record
Written By Nazifa Alam
The DDoS 2019-2020 statistics from Kaspersky regarding distinct changes in the frequency of certain types of DDoS attacks are a clear sign that these attacks aren’t going away. It was found that SYN flooding not only reached its highest record of 92.6% but also a displayed sign of continual growth, putting this in the “red alert” category for many IT teams.
It is without a doubt highly important to stay on top of SYN flood attacks in terms of method and countermeasures. To do this, cybersecurity professionals must understand the attack type, understand the tell-tale signs, and know-how to react quickly.
Multiple Ways a Hacker Can Implement an SYN Flood Attack
Although there are various methods to launch an SYN flood attack, the central aim lies in keeping the targeted server as busy as possible for as long as possible. To achieve this, the hacker ensures that all SYN/ACK packets sent by the targeted server go unanswered. If the device used to implement the attack does send an ACK packet, the response is wiped from the SYN backlog.
If a device receives an SYN/ACK packet from a server without previously sending an SYN packet to that server, the device will respond with an RST (reset) packet, cutting the connection. To prevent this, hackers retain open the largest possible number of half-open connections on the server.
SYN flood attacks can be carried out in the following ways:
- Direct SYN flood attack
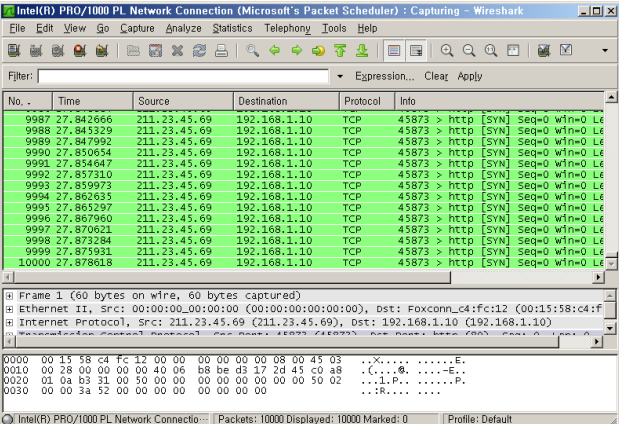
In this form of attack, the hacker uses their own IP to send multiple SYN requests to the targeted server. The server then responds with SYN-ACK which is then ignored while the attacker continues to send new SYN requests to the targeted server.
The victim server’s resources are used up with a half open connection session, leaving the server unable to properly function, leading to requests from legitimate users to be rejected.
Since this type of attack is committed by attackers using their own IP address, it is highly detectable and therefore, less likely to be used.
- SYN flood attacks using spoofed IP addresses
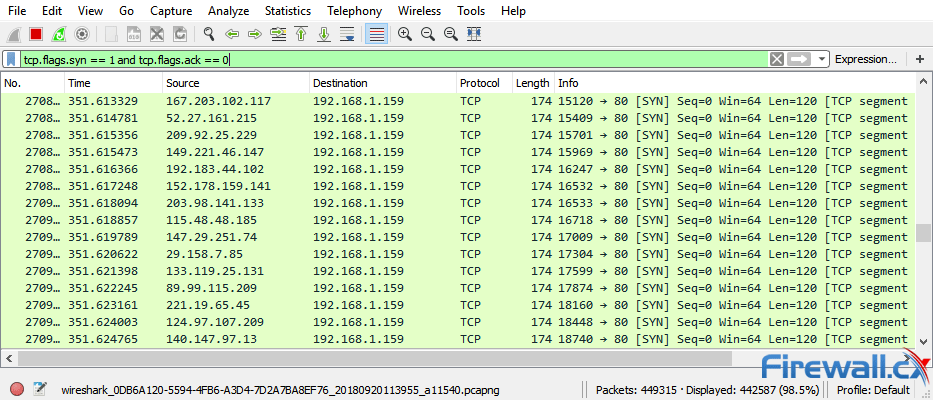
To avoid being discovered, hackers use spoofed IP addresses to send the numerous SYN packets. This in turn leads to the targeted server sending the SYN/ACKs to the spoofed IP addresses from where the server then waits for a response. As these requests come from spoofed sources, no response is detected.
Attackers tend to use IP addresses which are not currently in use to prevent accidently affected systems from responding with an RST packet which would halt the connection.
- DDoS (Distributed Denial of Service) SYN Flood attacks
This method of attack is carried out simultaneously by numerous devices as a part of a botnet design. The devices apart from the botnet are used by the attacker to send an overwhelming number of SYN packets to the targeted device. On the victim end, it could look very similar to a type 2 attack – SYN flood attacks using spoofed IP addresses.
- Reflection SYN flood attack
This form of attack involves the attacker spoofing the victim’s IP address and beginning a DDoS SYN attack against one or more uninvolved servers. These servers then respond to each of these SYN packets, causing the network traffic to multiply, resulting in the victim’s device becoming overloaded with SYN packages and unable to function.
How to Stop an SYN Flood Attack
One of the main characteristics of an SYN flood attack is the inconsistent loading time and loading list:
netstat -an | grep SYN_REC (REC representing the long list)
netstat -n -p|grep SYN REC|wc -1 (which gives the number of SYN attacks)
Checking the access_logs is also highly beneficial if a specific IP(s) is found to be requesting the most, which can be counteracted by blocking those IP addresses.
The multiple options below are available:
iptables -A INPUT -p tcp –tcp-flags ALL NONE -j DROP
iptables -A INPUT -p tcp –tcp flags SYN,FIN SYN,FIN -j DROP
iptables -A INPUT -p tcp –tcp-flags SYN,RST SYN,RST -j DROP
iptables -A INPUT -p tcp –tcp-flags FIN,RST FIN RST -j DROP
iptables -A INPUT -p tcp–tcp-flags ACK,FIN FIN -j DROP
iptables -A INPUT -p tcp –tcp-flags ACK, PSH PSH -j DROP
iptables -A INPUT -p tcp –tcp-flags ACK,URG URG -j DROP
The following commands can also be of use:
- KeepAlive on – To allow or disallow insistent connections.
- MaxKeepAliveRequests 100 – To allow a certain maximum number of requests.
- KeepAliveTimeout 15 – To enforce a waiting time of a few seconds until the next request can be sent in.
Mitigating SYN Flood Attacks
There are a few approaches that offer some level of protection against SYN flood attacks, some of which are server-based and some of which are cloud-based.
- Increasing the SYN backlog queue
Each OS is assigned a certain level of space/memory to hold half-open connections. Once the limit is reached, the connection is dropped. This approach is helpful for buffering smaller-sized SYN flood attacks while avoiding legitimate connections from being rejected.
- Recycling the oldest half-open connection
Another approach is to delete the oldest half-open connection to reuse the memory of the SYN backlog. This creates space for new connections to be formed, ensuring that the system to an extent, remains open for use in the case of a flood attack. This approach is not effective against high-volume SYN flood attacks.
- SYN cookies
This method involves the server creating a cookie. To avoid a connection being dropped in the case of the backlog filling, the server responds to each connection with an SYN-ACK packet whilst dropping the SYN request after sending the request. By removing the SYN request, the port is left open and available for a new connection.
If the connection request is legitimate, a final ACK packet is sent from the client-server which is then response to with a constructed SYN backlog queue entry. In this case, although some information regarding the TCP connection is lost, legitimate servers are not denied service during an attack.
- Firewall filtering
A firewall can be enabled to detect and filter SYN packets in addition to scanning for unauthorised port scanning. Enabling a firewall can help to prevent flooding and packet sweeps from occurring.