The terrifying reputation of the dark web has been enough to scare the average person into steering clear of it. Who is out there? What are they trying to push? Will I have my identity stolen just for downloading Tor? Well, the truth is that a lot of bad things do happen on the dark web. But a lot of the information we’re told about the dark web (and its often-confused counterpart, the deep web) is a fabrication or an exaggeration. In truth, these places range from innocent uncrawled private spaces to massive drug operations.
Because the dark web is one last retreat for people searching for cyber-freedom, that does also play a part in the genuine criminal underbelly. That’s why you should have tools to scan and understand what is happening out there. And the OSINT framework has numerous processes that we can undertake, including:
- Dark Web Clients Identification
- Dark Web Discovery
- TOR Search
- TOR Directories
- IACA Dark Web Investigation Support
This week, coming in at number eight, we’re looking at an interesting automatic threat updates tool – Hunchly Hidden Services Repository.
Hunchly
Unlike our other tools that we’ve looked at, Hunchly is a pretty robust and versatile toolset. It is perfect for tracking activities on the dark web because it uses open-source intelligence to create daily dark web reports that are relevant to your needs. Although you will probably be mainly concerned with the Hunchly cybersecurity bundle, there are also alternative provisions for law enforcement, private investigators, and other fields.
Signing up for the Hunchly daily update is an easy way to keep on top of the newest developments as they emerge from the dark web, but that’s not the only thing Hunchly can help you with.
Hunchly Dashboard
If you choose to install the Hunchly dashboard (which is available for free for 30 days), you can get access to personalized scanners and find the information that is relevant to your needs. Obviously, the dark web is a vast place – one which we barely understand in totality. But using this specific tool can help you to cut down the noise from the signal and acquire the information you need.
Installing it is easy and there are multiple ways to use the Hunchly toolkit which will help you in your day-to-day work life.
Using Hunchly Dashboard
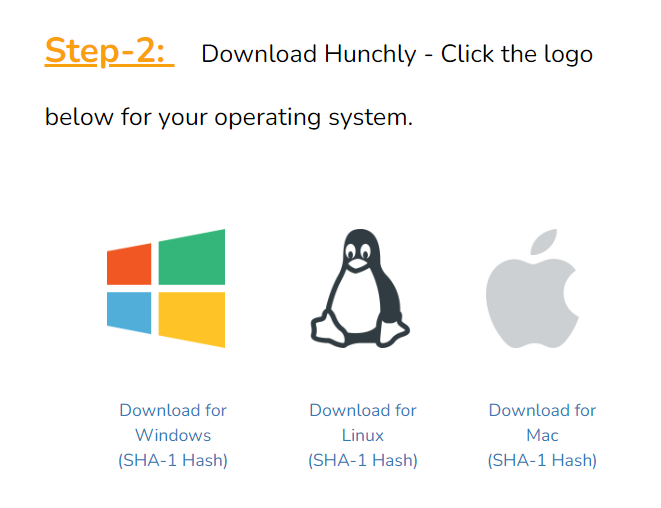
This process is a straightforward click and install that is available for Windows, macOS, and Linux. All images included from this point onwards came from the Windows installation.
- Download
When you click on the download button, you are sent to a quick walkthrough on how to get the programme on your machine. Hunchly advises that you use Google Chrome to install the dashboard, but any Chromium-based browser seems to work fine. There is a simple three-choice selection of buttons which you can match to your system.
- Get your license
After this point, you’ll need a temporary license to use the software. By signing up for Hunchly, you will receive an email which has the license key attached. In the installation wizard (or the equivalent installation process), enter the key when prompted. This should have the date included, so you will know when the license will expire.
- Set up Hunchly
Despite this section being about setting up the programme, there is very little to actually set up. Hunchly has a simple interface which has a few options for information input.
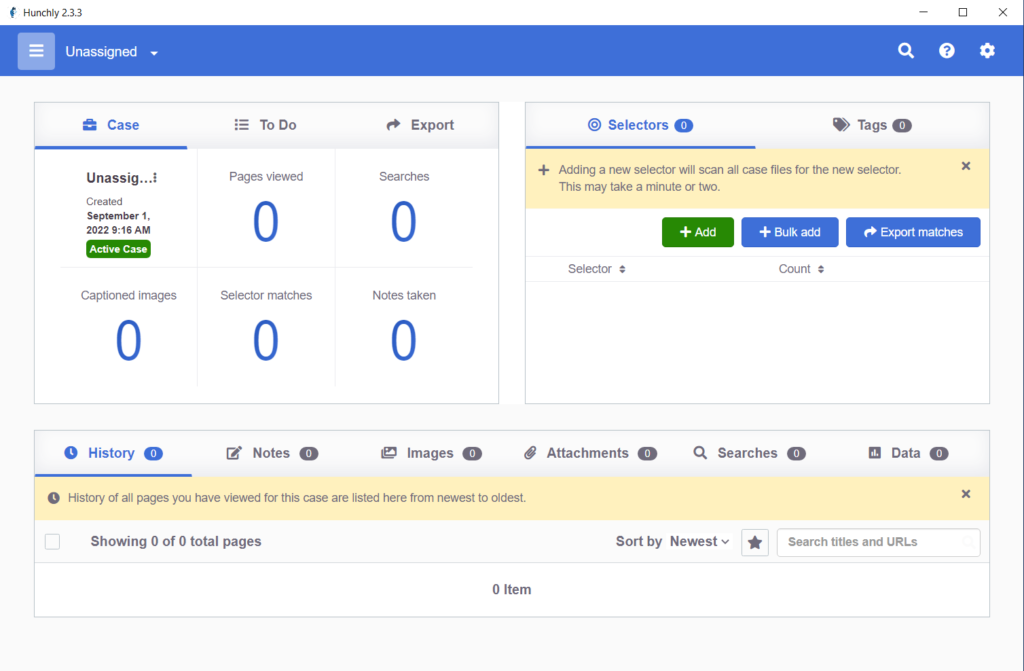
The cases that you are analyzing are displayed on the left-hand side and the selectors are on the right. Under these windows, there is a section for covering everything else you will need from the software – history, notes, images, attachments, searches, and data. All that on one interface. Very clean, very intuitive, very useful.
- Hunt
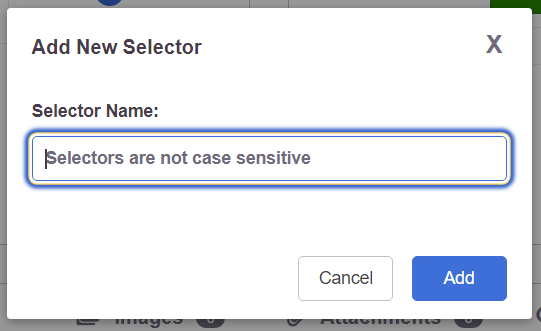
When the application is installed and you have had time to play with the interface, clicking the Add button in the Selectors menu allows you to add case files and sources to Hunchly’s workflow. This will allow you to collect relevant information about the issue you are working on and create stronger defenses against the adversary.
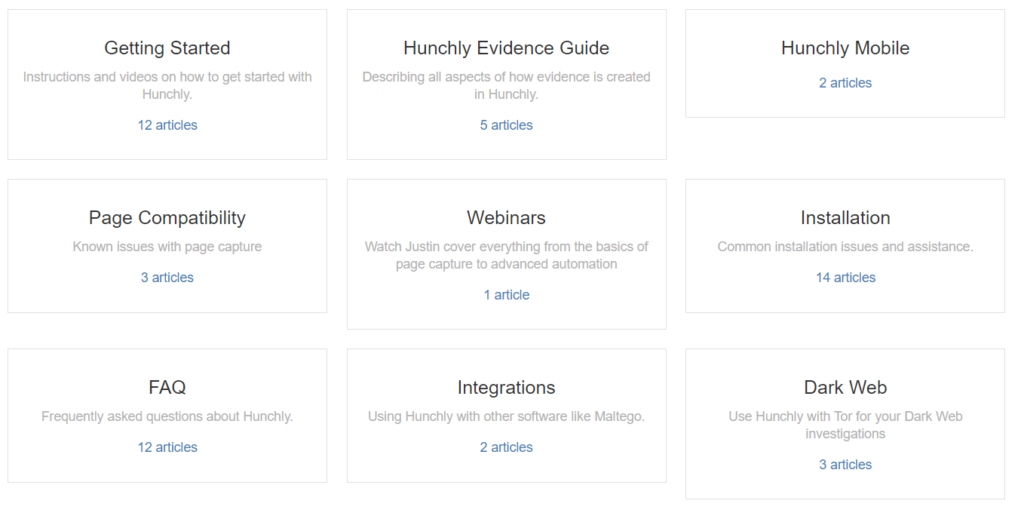
Because Hunchly wasn’t designed with just cybersecurity professionals in mind, there is a rich toolkit that will go beyond the scope of what you will probably need most days. However, the Hunchly knowledge base is full of useful guides and tutorials to help you either perfect what you need or utilize a set of tools that you wouldn’t generally associate with purely organizational-minded cybersecurity work.
Hunchly is a fantastic tool that our team has enjoyed playing with. It’s simple, effective, and does more than we would need to successfully gather threat intelligence, meaning that there is almost certainly something useful for everyone in the toolkit. If nothing else, it’s free for 30 days and is a lightweight dashboard – you’re not losing anything by signing up for it and you can use it as a launch pad for understanding what you do need.
If you’re already using Hunchly or are intending to use it, remember that it’s not the only tool out there. Hunchly uses a massive database of crowdsourced threat intelligence to help us understand the dark web and what’s out there lurking. But before we can look to the cyber-world around us, we have to make sure we’re locked down at home too. Here’s Indra, writing about how we can use Go spider to build our understanding of our websites, hunt for threats elsewhere, and stay a step ahead of threat actors.








