How to Perform Threat Hunting during an Incident
Post Credit: Ricoh Danielson
Have you ever thought about looking for the ongoing threat when you’re working on a live incident? Wouldn’t it be great to know in advance what the threat actor is looking for and how we can control their movements without being noticed?
If that interests you, then this article is all about streamlining the threat hunting process while responding to an incident.
How Threat Hunting works during an Incident Response
Threat Hunting during a cyber incident pays dividends. The image is in a position where you chase a threat actor without noise or sounds. It is quite hard to find out where the threat actor is poking in and what they might be doing next but understanding Threat Hunting during a cyber incident would be more valuable to businesses of any size.
So how can we do Technical Threat Hunting during a cyber incident? Let’s find out!
Investigating active incidents: Technical requirements
So, how do we conduct threat hunts and what tools do we need to use? We can do this either manually or with automation. If there is a budget for tools such as Splunk, Crowd Strike and or CyBorg then we can make use of the resource. Let’s take Splunk for example from Cyborg when it comes to SolarWinds.
Example String: SunDust Known Malicious DNS
Splunk
(query_type IN (“CNAME”,”A”) AND (query=”*avsvmcloud.com” OR answer=”*avsvmcloud.com”)) OR (query_type=”A” AND query IN (“deftsecurity.com”,”freescanonline.com”, “thedoccloud.com”, “websitetheme.com”, “highdatabase.com”, “incomeupdate.com”, “databasegalore.com”, “panhardware.com”, “zupertech.com”, “freescanonline.com”, “deftsecurity.com”, “thedoccloud.com”))
| stats values(_time) as occurrences count by src, query, query_type, answer
| convert ctime(occurrences)
Using the extracted string we can drill down into known tactics, techniques, and procedures (TTP) and Indicators of Compromise (IOCs) that the threat actor used during the exploit. We can break out from the string of the different Command & Control (C2) call out or call backs.
Sunburts Named Pip IOC
Splunk
index=sysmon sourcetype=sysmon:xml (EventID=17 OR EventID=18) PipeName=”583da945-62af-10e8-4902-a8f205c72b2e”
| stats values(_time) as occurrences, values(EventID) as eventID, values(PipeName) as pipeName count by host
| convert ctime(occurrences)
From this string, more information of the known Event ID can be extracted to allow searching through EVTX logs faster. Although EVTX research seems to take a long time, it would be of great help.
These are great search strings provided by a vendor that can help with a speedy and timely threat hunt which will allow for faster mitigation.
Manual Threat Hunting
Manual threat hunting is when there are no tools. Many small to mid-size organizations may find themselves in this predicament due to small tool budgets and or no budget. The cyber security professional will have to conduct these manually.
This is where old-school Digital forensics comes into play. The cyber security professional will need to conduct RAM dumps and images of the device in question. After which locating the EVTX logs along with extracting them will be needed.
Something to consider: EVTX logs and some of their format is non-cohesive or non-consumable to the cyber security researchers so here we need to do the manual grepping to categorize all these data.
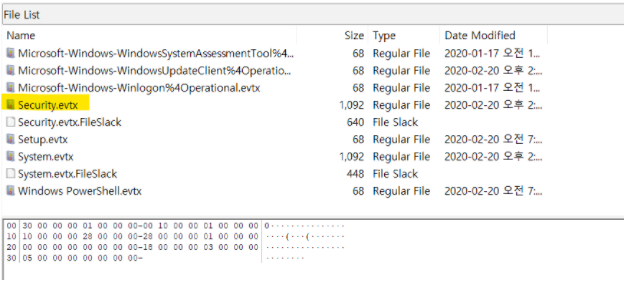
Manually grepping EVTX logs might look something like this.
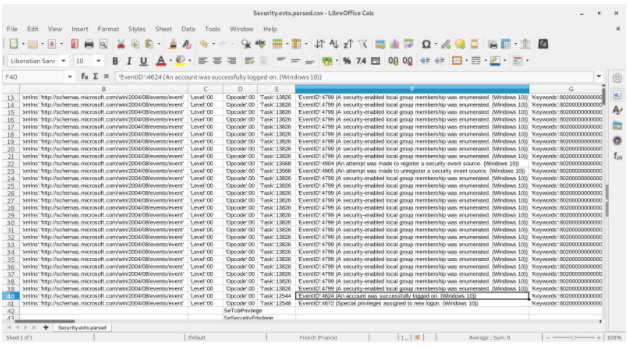
Reviewing findings from active threat hunts during an IR
Now once we have completed this step by grep-ing the EVTNX logs, now the threat hunt can start. This is where we are going to have to roll up our sleeves and dive into the logs in more detail.
Understanding the event logs, and extensions such as WMI along with the others in which these were executed can provide a lot of information about the threat actors’ action, where the threat actor came from, and where they might be going next.
Why choosing manual process over tolls might be a clever idea
Sometimes tools will only take us so far. Tools are great to have when we need amplification in the process like how fast and effective, we might be able to be. On the other hand, the tools will only take us that far.
Manually doing threat hunting gets you in the weeds with the threat actor and allows for more hand-to-hand combative. This intimate approach reveals the true technical details of which threat actor you might be dealing with and what degree of expertise the threat actor might be.
Steps for Accessing Threat Hunting in the Cloud
More than likely there will or is a time for cloud threat hunting, it really depends on the in-depth attack approach from the threat actor. If we find ourselves in a cloud environment combating a threat actor, then the same premise might apply.
Either in the cloud or locally, logs and logs grepping will prove to be a means to finding the threat actor. In the cloud, there might be a different EVTX log or thereof an event log, so understand how to conduct logs forensics and network forensic will provided a lot of information and IOCs needed during a live threat hunt.
Summary – Perform Threat Hunting
There is a lot to unpack here. Having the means to conduct threat hunts is the most important takeaway. Either know how to do the manual threat hunt and or use a service provider of these threat hunts. If you do one before the other, then that is a good start but doing both at the same time will provide great metadata during the threat hunt.
The SecPro is a weekly security newsletter to help you stay sharp and upgrade your skills with trending threat insights, practical tutorials, hands-on labs, and useful resources. Build skills in as little as 10 minutes. Join the newsletter here.








