Using Cewl to create a custom wordlist
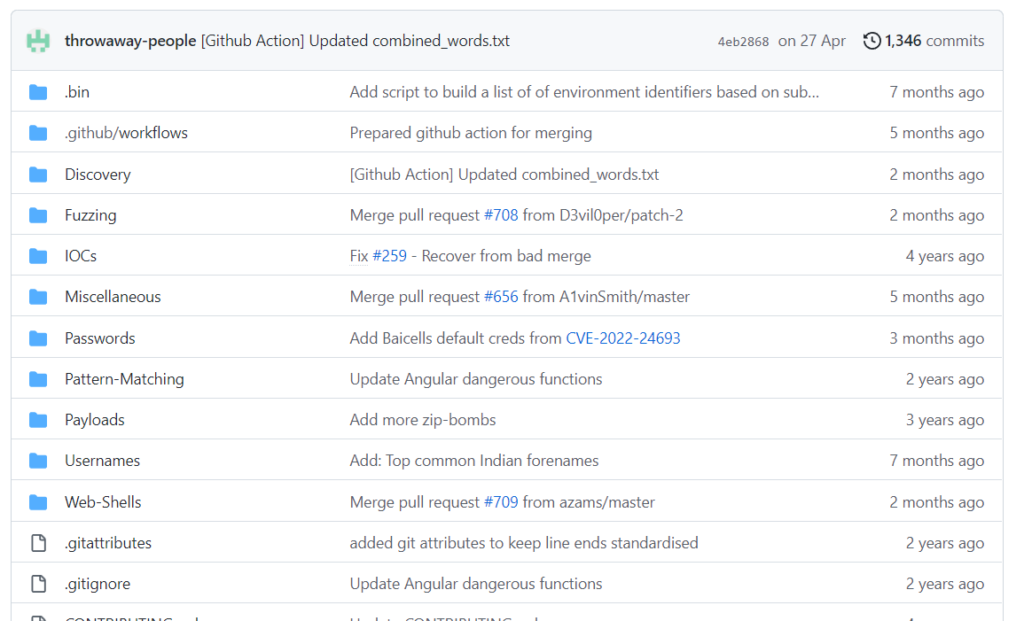
Every hacker has got a collection of wordlists. A different wordlist for a different purpose. A wordlist for username, a wordlist for a directory, a wordlist for password, etc. Also, many online repositories provide a huge list of community-curated wordlist. My favourite is the wordlist provided by Seclist.
Most password-cracking programs are only as good as the wordlist that you provide them. SecLists is the security tester’s companion. It’s a collection of multiple types of lists used during security assessments, collected in one place.
But sometimes the problem with using these wordlists is that they are general purpose wordlist and some applications have very specific passwords which these wordlist fails to get. For cases like these, we need to have a custom wordlist that is meant only for that particular application.
Today in this article we will discuss a tool that will help us create a custom wordlist for an application. Not all people are creative while setting passwords and often they end up putting a password that they are familiar with. For example – If someone is from a cryptocurrency background or works in the crypto industry then they are more likely to use words for passwords that are used in their industry, such as bitcoin, crypto, web3, blockchain, Ethereum, etc. Similarly, people in the sports-related industry will most likely use words like cricket, football, Ronaldo, game, etc. You get the point.
It’s normal human nature to use the words that we use in our everyday life as those words will first pop into their heads when considering passwords. And we can use this exact human nature to create a custom wordlist which we can then try out in brute-forcing passwords.
For making such a custom wordlist we will use a tool called Cewl. Cewl is a Ruby program that crawls a URL to a defined depth and produces a list of keywords that can be used as a wordlist. And it is highly effective.
Download Cewl from here: https://github.com/digininja/CeWL
Installation
CeWL needs the following gems to be installed:
- mime
- mime-types
- mini_exiftool
- nokogiri
- rubyzip
- spider
The easiest way to install these gems is with Bundler:
gem install bundler
bundle install
Alternatively, you can install them manually with:
gem install xxx
The gem mini_exiftool gem also requires the exiftool application to be installed.
Running CeWL in a Docker container
To quickly use CeWL on your machine with Docker, you have to build it :
- Build the container :
docker build -t cewl .
- Container usage without interacting with local files :
docker run -it –rm cewl [OPTIONS] … <url>
- Container usage with local files as input or output :
# you have to mount the current directory when calling the container
docker run -it –rm -v “${PWD}:/host” cewl [OPTIONS] … <url>
If you are finding it hard to install it, then I have good news. This tool comes pre-installed in Kali Linux.
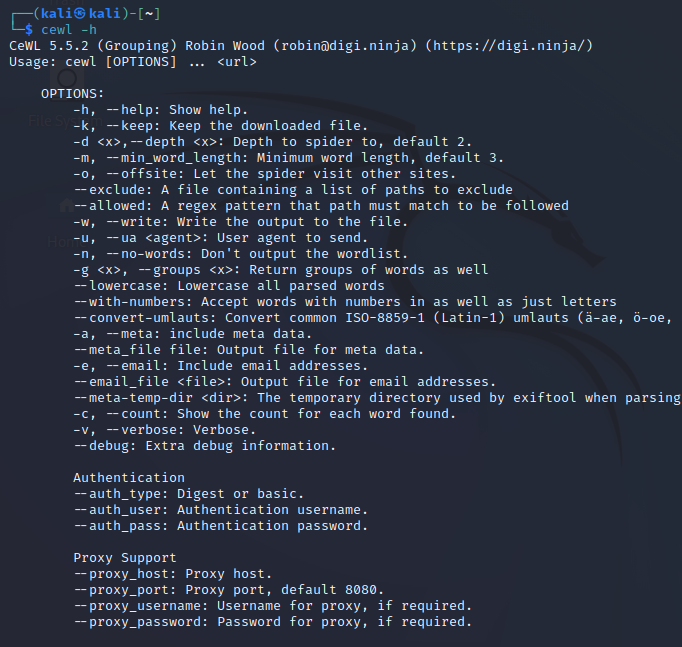
Open the terminal in your kali Linux machine and type cewl -h and it will show you all the options
Cewl default usage :
Use the following command to spider the provided URL and make a custom wordlist from the website. In this example, I’ll use the website https://www.packtpub.com/
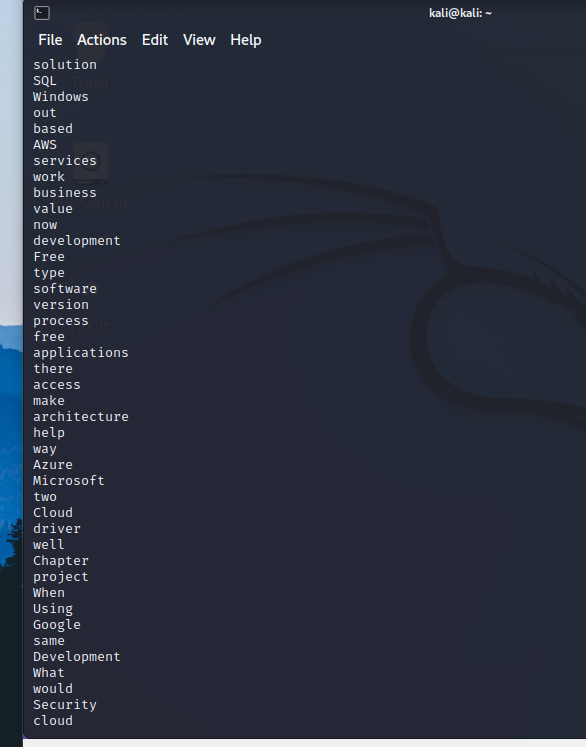
As Packt is a book publishing company that focuses on IT and security so you can see the words are related to IT and security.
Saving Wordlist as a file
Cewl has an option that allows users to save the keywords in a file so that the file can be used in password cracking tools. Run the following command to save it in file
cewl https://www.example.com/ -w wordlists.txt
Creating a Certain-Length Wordlist:
Sometimes we may know the length of the password or we might want to eliminate words like is, at, the, etc from the wordlist. For this, we have an option ‘-m’ to define the length of the word. We can run the following command to do it.
cewl https://www.example.com/ -m 7
Conclusion
Cewl is a feature-rich tool. It provides many more features which I have not covered in the article. A custom wordlist is very helpful when testing for real-life applications. It helped me a lot in my pentest and I’m sure it will help you as well.








